Knowing That You Only Have Telnet
In my previous post about Telnet entitled, "Using Telnet to Perform Tasks" you discovered how to use Telnet to work interactively. At present you have enough information to view some of the security issues with Telnet. It's incredibly easy for someone to monitor your Telnet session. The only protection you have is firewalls and other security y'all might have in place—Telnet is completely open up and offers nix in the way of security. Lack of security is 1 of the reasons I didn't cover this utility in the "Windows Command-Line Administration Instant Reference." (Telnet is covered from a command line perspective in "Administering Windows Server 2008 Server Core.") Yet, the lack of security isn't a problem in some situations and many administrators prefer to use Telnet to manage some network hardware such as switches and routers. Consequently, the main emphasis of this post is edifice an sensation of the security issues behind using Telnet and so that y'all tin make a adept determination virtually using information technology to meet your needs.
Earlier you lot can see the security issues for yourself, yous need to download a utility to sniff packets on your network. This post will rely on a free utility named Wireshark because information technology does the job admirably and is supported on a number of platforms. Considering I'm using the 64-scrap version of Windows 7, I downloaded the 64-fleck Windows installer for the one.iv.7 version of Wireshark. To make things unproblematic, I performed a full install. Part of the Wireshark setup volition too install WinPcap, so you don't need to install this product separately. If you're using some other version or configuration of Wireshark, your screen may not look precisely like mine.
Using a sniffer is somewhat dangerous and you demand administrator privileges to exercise it. This post isn't designed to make you an proficient in protocol sniffing. In fact, this mail service is uncommonly simple and is designed but to make you enlightened of deficiencies in Telnet security. The nefarious individual who gains access to your network to sniff most will have significantly more than skills and be able to learn considerably more than yous'll learn using the uncomplicated directions in this post.
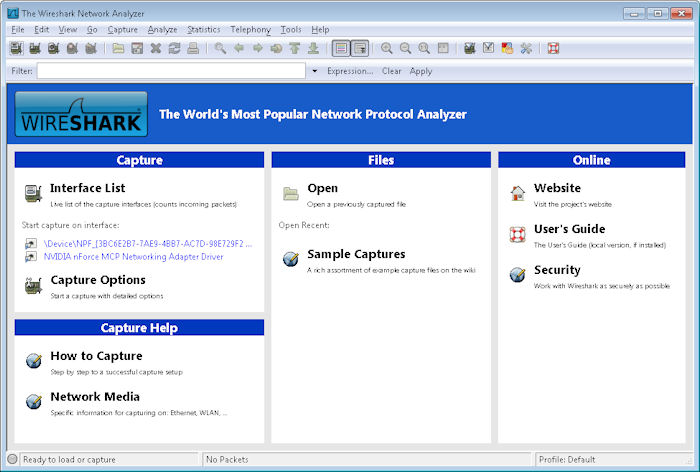
Afterwards you complete the installation, you'll exist able to kickoff Wireshark. Choose Start > All Programs > Wireshark and you'll see the initial Wireshark display shown hither.
Wireshark isn't configured to work with Telnet at the outset, so you need to tell it what to sniff. Click Capture Options and yous'll see what looks like an incredibly complex Capture Options dialog box like the one shown here.
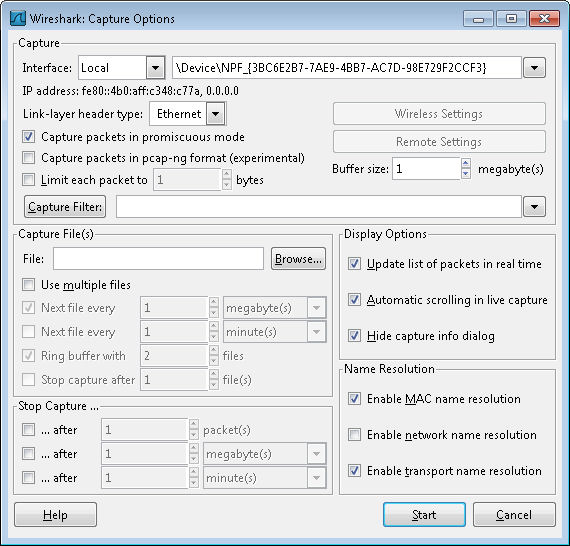
We're not going to worry virtually the vast majority of these options. In fact, you just need to set ii options to sniff out Telnet packets. Look first at the Interface field. Brand certain it's set to Local. Select your network adapter from the driblet down list box. The network adapter will normally have a human readable name, not something odd equally shown in the screenshot.
Next you need to tell Wireshark what to sniff on the interface you've selected. Click Capture Filter. Type Telnet in the Filter Proper name field and port 23 in the Filter String field. Click New. Your dialog box should look like the one shown here.
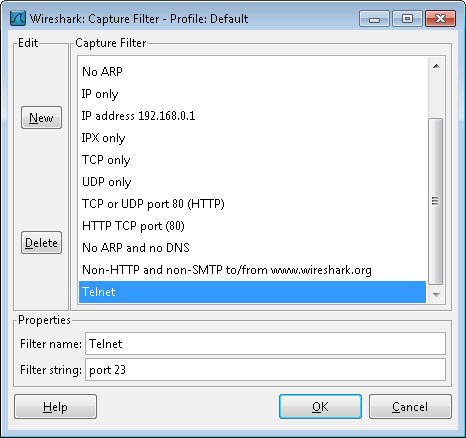
Click OK. Y'all'll encounter the filter criterion entered in the Capture Filter field. More importantly, Wireshark is now configured to offering a Telnet filter anytime you demand one. Click Get-go. The Wireshark display will change, only you won't see anything on it—the display will be blank.
Open a command prompt and start a re-create of Telnet in interactive mode. Make sure you open a control prompt with administrator privileges. The human action of starting Telnet won't create any packets every bit you lot tin see in Wireshark. In fact, type ? and printing Enter. You lot'll run into that Telnet is still perfectly safe—it isn't generating any packets.
Employ the Open control to open a connection to your server. Simply typing O ServerName and pressing Enter generates packets. You lot can see them in Wireshark like this:
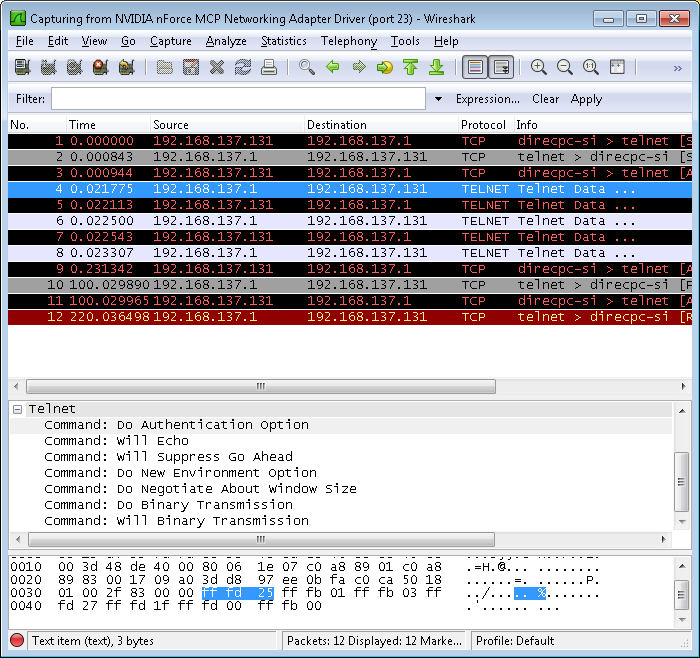
Discover that some of these entries are labeled Telnet Information. In improver, the Source and Destination columns tell you which direction the information is flowing (the client is 192.168.137.131 in this case). Click on the start of these entries and you'll come across that the center panel contains some information about the Telnet Data. Open the Telnet entry and yous'll see some interesting information as shown in the figure. For instance, the packet information tells the viewer that Telnet is set to use the hallmark option.
Go back to the command prompt now. Type y and press Enter to send your password information to the server. Of grade, ane of the big questions y'all probably have is whether Telnet is exposing your username and password. Near the end of the packets, you'll notice i that contains an Suboption Begin: Authentication Option entry like the i shown here.
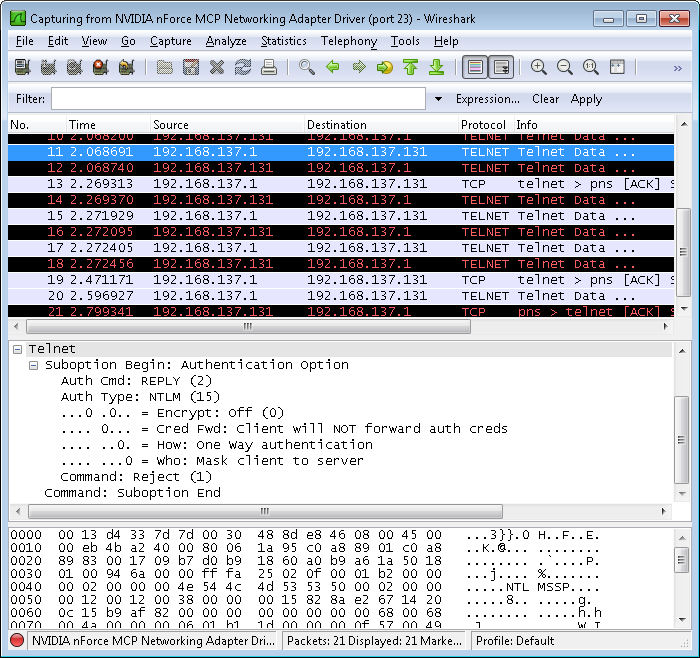
In this case, the option entry tells the server that the client won't forward the authentication credentials. The choice works because I'm already signed onto the server and the server already has my credentials. This is one of the items you'll want to check for your own Telnet setup, however.
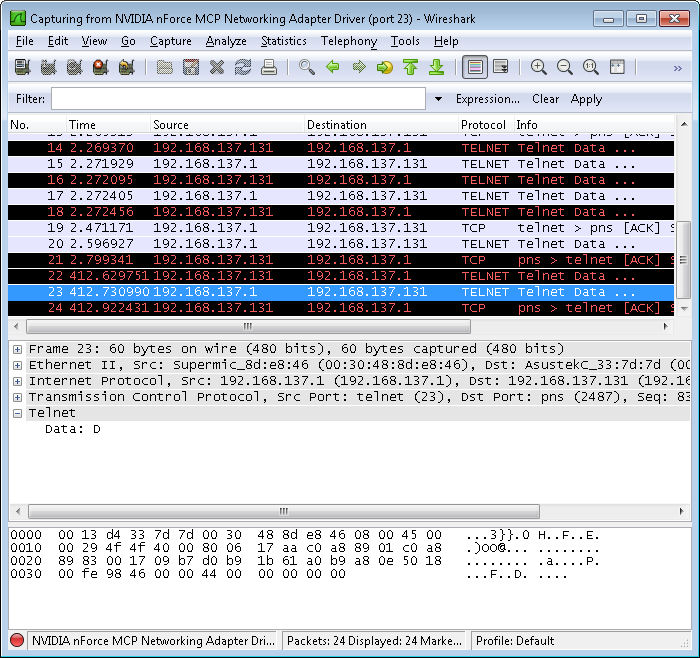
Unfortunately, this session isn't safety by a long shot. Type only a single letter, a D, at the command prompt. You'll notice that typing this single letter of the alphabet generates a bundle that you tin can see with Wireshark like the one shown here.
In fact, you'll find that every action on your office creates more packets—each of which is easily sniffed past anyone with Wireshark or any other application of the sort. Terminate the command by typing ir and pressing Enter. You'll see the expected response at the command line.
At this point, y'all tin can also see the response from the server in Wireshark. The text isn't as readable considering it contains all of the control characters normally used to format the text. However, here'due south an example of the response as it appears on my system.
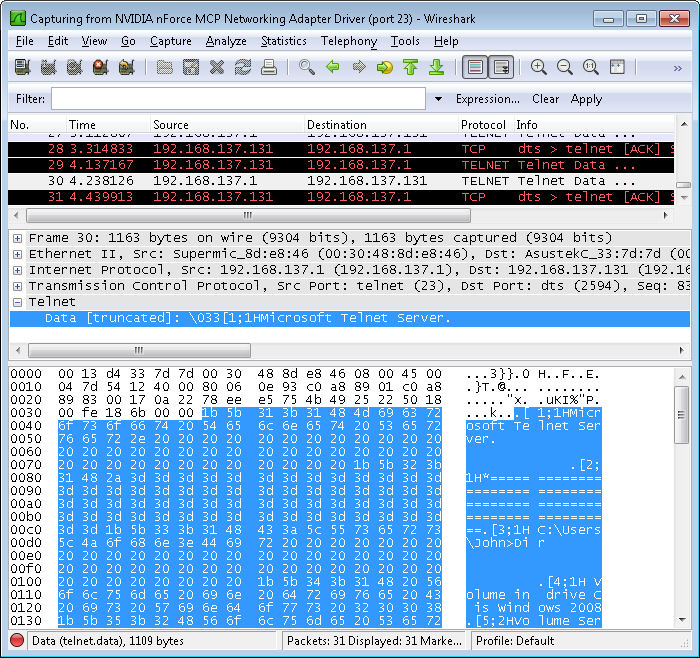
Look at this response carefully and you'll see that anyone can learn precisely what you're doing. If yous have to enter passwords to perform a item chore, the viewer will go them too. Telnet isn't a secure method to manage annihilation—you lot need to provide a secure environment in which Telnet can run. This mail only touches on the tip of the iceberg, of course. Let me know if you have any questions well-nigh it at John@JohnMuellerBooks.com.
Source: http://blog.johnmuellerbooks.com/2011/06/07/sniffing-telnet-using-wireshark/
0 Response to "Knowing That You Only Have Telnet"
Post a Comment